
DMARC Adoption in U.S. and Canada Higher Education Sector
Phishing attacks are an immediate and growing threat to higher education institutions where sensitive data and susceptible audiences are targeted by cybercriminals who use AI to create fraudulent, albeit convincing, campaigns.
In this installment of our adoption research in higher education, we’re looking at how DMARC adoption is shaping the email security landscape of North America. We inspected the parent domains of the top colleges and universities in Canada and the United States based on the number of employees to access the publicly available DMARC, SPF and DKIM records published in the DNS.
On any campus on any given day, it’s common for students, staff and faculty to receive a warning from their school’s IT department about emails that appear to be real but are indeed fake. Campus community members can easily be tricked when they receive an email asking them to login, update their email password, pay an invoice, update direct deposit information or provide other information that leads to credential theft. Since the email is seemingly coming from a known entity, people trust that the message is legitimate.
Colleges and universities are high-value targets for cybercriminals and vulnerable to phishing and social engineering attacks. They hold a trove of intellectual property; student, faculty, staff and alumni records; financial data; and fundraising records. Additionally, the increased use of social media learning management systems equate to a broader, more difficult-to-protect attack surface with numerous entry points.
One of the challenges for the education sector is tech sprawl, specifically related to the use of vendors where email is part of their value add. In the majority of cases, we see a variety of services being utilized for the same purpose, and this lends to the sprawl—like using five different bulk mailers when one could be leveraged. To be fair, this is a bit of a visibility (and shadow IT) issue; that is to say that the folks using Mailchimp in a math department were not aware that an account already existed for a similar bulk mailer.
Additional challenges lurk under the surface due to numerous instances of the same service. For example, I worked with a university several years ago that had over 100 instances of Constant Contact. The result is a need for a deeper level of investigation as it isn’t always straightforward to identify the multiple account owners related to a single source of email; that identification is necessary for remediation. IT staff having access to human-readable DMARC data is a critical first step to seeing what’s used and building a game plan for next steps.
Tech sprawl, numerous domains generating email for staff and students, SPF management and so on can be daunting. The good news is that with motivation, planning and persistence, the domain catalogs for these institutions can be brought into DMARC compliance and enforcement.
—Fred Bianchi, Director of dmarcian US Business Unit
Higher Education Breaches in the Americas
Earlier this year at the University of Texas at El Paso (UTEP), cybercriminals posing as UTEP officials sent phishing emails to students. The phishing exploit resulted in bank credential harvesting; subsequently, student credentials were leveraged to redirect thousands of dollars, much of which was student aid, into fraudulent accounts. UTEP is offering emergency relief funds for students that were affected by the phishing attack.
Powerschool, a large provider of educational cloud-based software in North America, was breached using stolen login credentials. Personally Identifiable Information (known widely as PII) was stolen, including email addresses, and thousands of account holders were warned to be on the lookout for fraudulent messages sent to the stolen email addresses.
Immediate impact of a cybersecurity incident in a school may result in disruptions to teaching, learning and critical business operations. Many school districts that have experienced a cybersecurity incident speak to the significant, wide-ranging costs of a cyber incident:
- Financial: costs attributable to teaching and learning loss; labor costs resulting from a shift to manual execution of operations and processes that, in normal conditions, are automated (e.g., manual writing of payroll and third-party vendor payments, etc.); legal and insurance expenses; and long-term costs like credit monitoring for impacted individuals, etc.
- Political: Loss of trust among teachers, parents, and the community.
U.S. Department of Education
DMARC Status of the Top 500 US Institutions of Higher Education
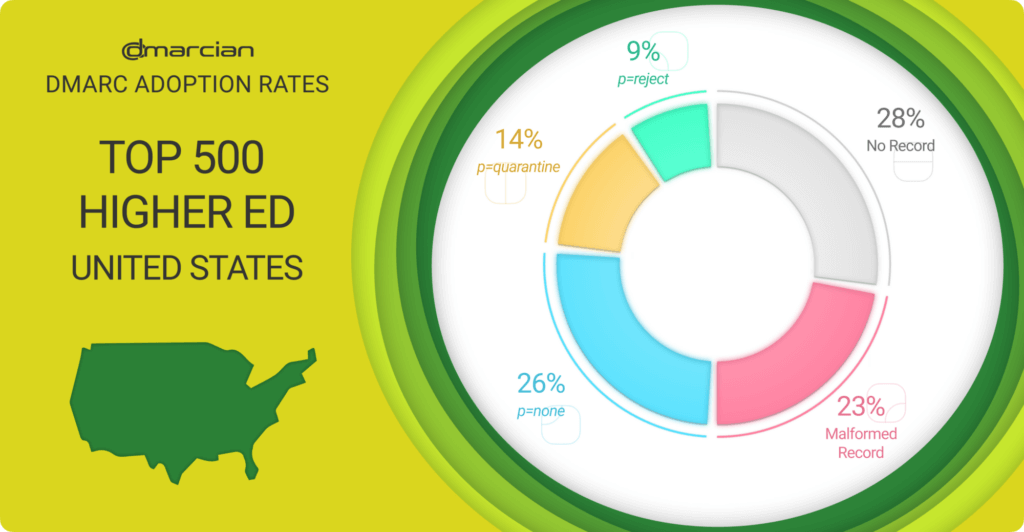
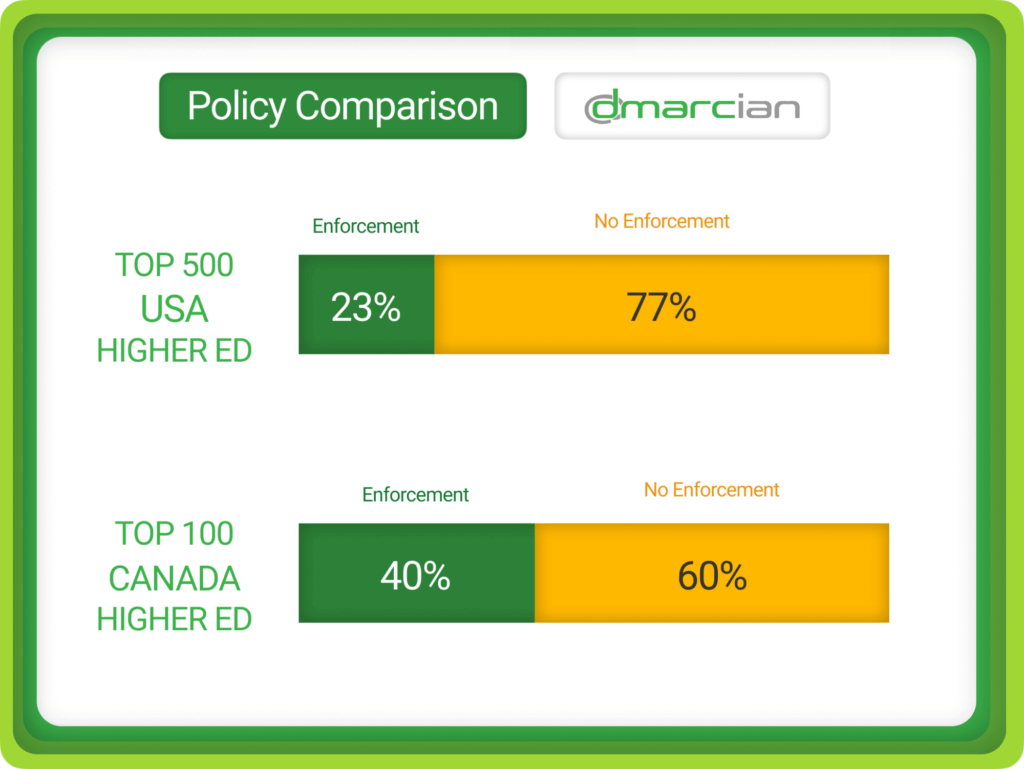
What we see in the top 500 higher education institutions in the United States is that 77% of parent domains are not protected from being used in email exploits because they have no DMARC record, have mistakes in their records or have a DMARC record with a p=none policy, the monitoring phase that doesn’t affect email delivery. Only 9% are fully protected by DMARC policies at p=reject, while 14% reside at a p=quarantine policy where failing emails are sent to spam folders.
Following are the full results:
- 28% have no DMARC record.
- 26% have a record at the p=none monitoring phase.
- 23% do not follow best practices, leaving domains exposed or without visibility.
- 14% have a DMARC policy of p=quarantine, the penultimate policy progression before p=reject.
- 9% are at p=reject, taking full advantage of the protection DMARC offers.
SPF Record Issues
We’ve found that when deploying DMARC, developing and publishing SPF records often cause confusion. The most common problems we saw with this set of domains revolved around SPF. Perennial issues such as too many DNS lookups, multiple SPF records, lack of an SPF record or invalid records (typically pointing to syntax errors) are commonplace.
Review these guidelines to help publish accurate, secure SPF records.
DMARC Status of the Top 100 Canadian Institutions of Higher Education
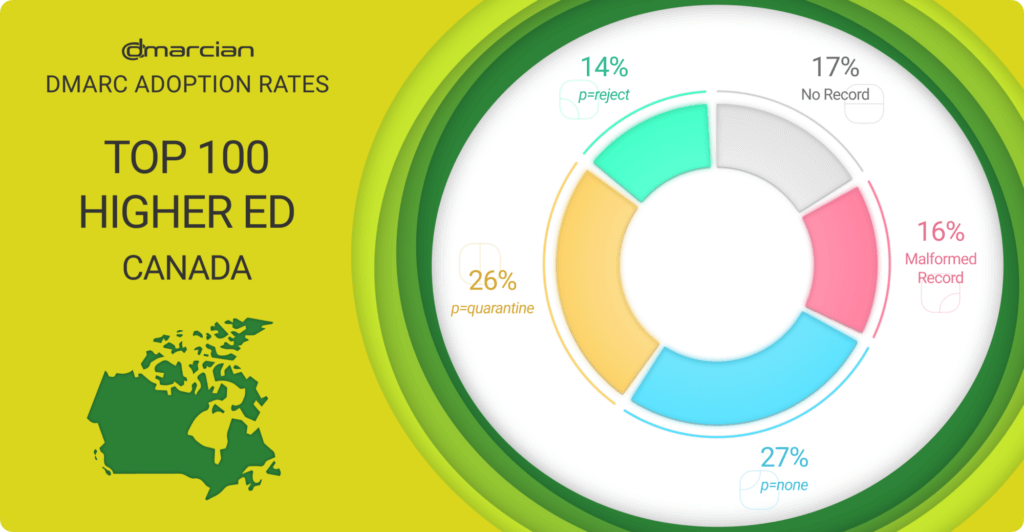
With 40% of domains at the DMARC enforcement policy levels of p=quarantine or p=reject and a total of 67% of the domains with DMARC records, Canadian colleges and universities are well on their way to creating a secure email landscape. That said, 60% of the domains are susceptible to being used for phishing exploits because they have no DMARC record, mistakes with their records or a p=none policy.
The optimists among us see the 27% p=none cohort as a group that is aware of the importance of the DMARC control and have begun their journey to enforcement. Others think that the group is resting on its laurels after establishing the monitoring policy to satisfy a sender requirement such as those instituted by Google and Yahoo.
Whatever the perspective, here’s what we found:
- 17% have no DMARC record.
- 27% have a p=none record.
- 16% have problems with their records.
- 26% have a p=quarantine DMARC policy.
- 14% are at p=reject.
Beyond its primary function of fraud detection, DMARC plays an integral part in cultivating trust within academic communities. Researchers, faculty members, and students tend to open and respond more favourably to emails sent from academic institutions with effective security protocols in place. As soon as recipients recognise an institution is using DMARC, they can feel assured that any communication from it is legitimate, decreasing their chance of falling prey to phishing attacks or similar attempts on email accounts.
In turn, this enhances academic communications security and creates a safer environment for sharing research findings, collaborating with peers, and engaging in academic discourse. Furthermore, DMARC’s reporting function allows institutions to quickly detect threats, taking swift action to address emerging risks and limit potential damage.
We’re here to help US and Canadian schools
As DMARC adoption continues to grow and become recognized as the primary control to observe and restrict email domain usage, dmarcian is committed to help educators protect students, employees, alumni and donors from email fraud. We’re people helping people secure their domains from phishing and manage their email security for the long haul.
Want to continue the conversation? Head over to the dmarcian Forum.


