DMARC Status of Top 100 Global Banks
The last time we took a look at DMARC adoption for the top 100 global banks, Google and Yahoo hadn’t yet released their ecosystem-shifting sender requirements, COVID-19 was forcing organizations to transition to remote work and greater reliance on email communications, and AI was building steam with integrations. All this was happening while regulatory pressure to adopt DMARC was accelerating.
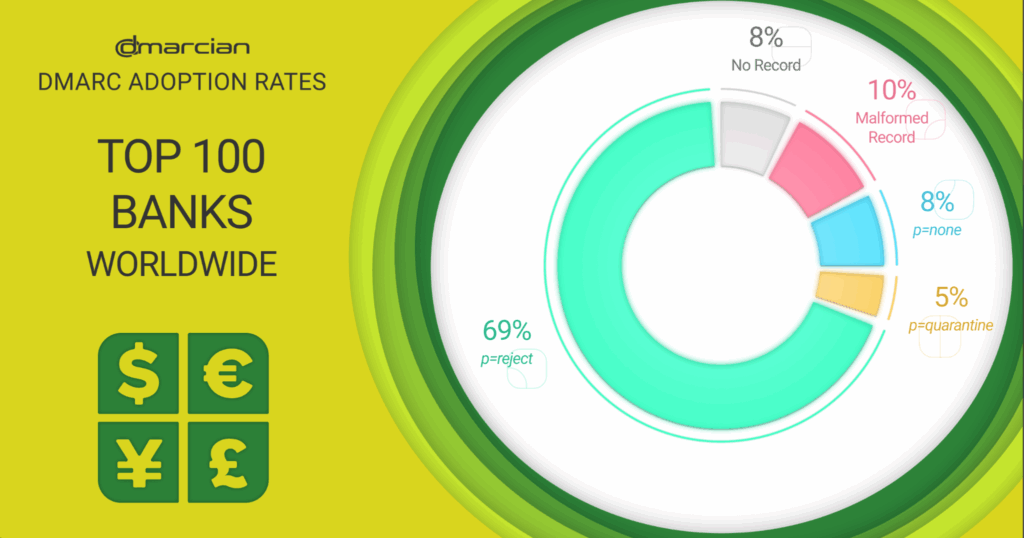
From 2021 to 2025, we saw the following trends in DMARC adoption for the top 100 global banks based on revenue.
- 74% decrease in domains with no DMARC record
- 52% decrease in p=none DMARC policies
- 17% decrease in p=quarantine policies
- 50% increase in p=reject policies
These numbers represent the strongest DMARC enforcement levels in sectors we’ve researched. A 74% decrease in domains with no DMARC record indicates that most of these banks have adopted DMARC as a foundational layer of email security. Fewer domains are lingering in the monitoring-only phase with a 52% drop in p=none policies, and a lower rate of p=quarantine likely points to banks advancing policy enforcement.
We were excited to see a 50% increase in p=reject policies—the ultimate goal of DMARC deployment. More banks are taking advantage of DMARC’s ability to block unauthorized emails and have committed to preventing phishing and domain spoofing at the highest level.
Learn how DMARC can help your organization meet the PCI DSS requirements.
SPF Record Errors
We also found that 10% of the top 100 bank domains had SPF record mistakes, namely a lack of SPF records. Though it’s a small percentage compared to other sectors, SPF record problems can negatively affect deliverability, create gaps in authentication and lead to reporting problems.
DMARC Benefits
Banks are using DMARC and its underlying technologies of SPF and DKIM as domain-based controls to address the following:
- Email Fraud – DMARC’s original use-case. DMARC provides visibility of how a domain is used and prevents unauthorized senders from sending email on behalf of an organization.
- Email Reliability – Organizations need email to be reliable. DMARC is the foundation for reliable email delivery, and is often the first step taken to resolve email delivery issues.
- Compliance – Industries, governments, and regulations are increasingly requiring DMARC to be in place. It is also becoming a requirement for many cybersecurity insurance providers.
These controls are more important than ever. In their most recent Phishing Activity Trends Report, the Anti-Phishing Working Group (APWG) noted that attacks against the online payment and banking sectors totalled 30.9 percent of all attacks. In the first quarter of 2025, APWG observed 1,003,924 phishing attacks, the largest number since late 2023.
Payment Card Industry DMARC Guidance
In advancing its cybersecurity standards, the Payment Card Industry (PCI) recommends email authentication in section 5.4.1 of PCI DSS v. 4.0.1. They ask organizations to employ a combination of approaches that include anti-spoofing controls like DMARC, SPF and (DKIM) to help battle phishing, impersonation and spoofing exploits. These anti-phishing controls are a best practice until March 31, 2025, when it becomes required and necessary to fully consider during a PCI DSS assessment. In addition, the DSS recommends that “anti-phishing controls are applied across an entity’s entire organization.”
Take a look at our DMARC adoption studies for other sectors.
How dmarcian can help
With a team of email security experts and a mission of making email and the internet more trustworthy through domain security, dmarcian can help you assess your domain catalog, deploy DMARC and manage domain security for the long haul. With our expertise and mission of DMARC for All, we can help you
- Progress safely from monitoring to enforcement with our expert guidance.
- Understand how SPF, DKIM and DMARC work, and why they are essential.
- Configure these protocols to ensure seamless email delivery.
- Monitor authentication reports to identify and resolve any issues promptly.
Want to continue the conversation? Head over to the dmarcian Forum.


