
Are your Google Calendar Invite Responses Blocked by DMARC?
We have previously discussed how Google Calendar invites and other Google applications are not capable of sending DMARC-compliant email using SPF.
There is also an issue for receivers who interact with Google’s email body invite links, as Google spoofs the invitee’s domain to generate a notification. If the invitee’s domain is at p=reject, this can occasionally send back a bounce to the invitee, making it confusing for everyone.
The Problem
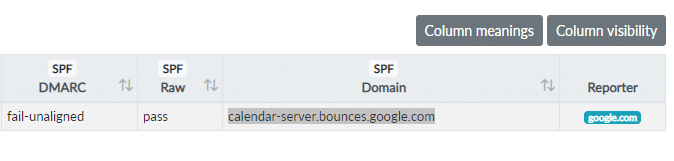
You may see Google as a source in your dmarcian dashboard while not being subscribed to their services. It would look something like this.
Google Calendar invites and DMARC are a known issue stemming from how Google handles calendar invites. When an invite is received, it contains Google-generated links in the body of the email calendar invite, combined with the calendar invite functionality provided by the email client.
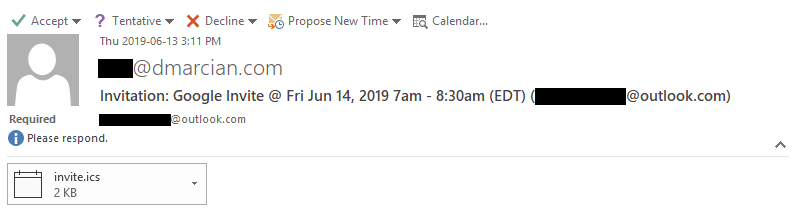
Depending on where you’re viewing an invite, you may see two ways to accept it. One way is using the “yes, maybe, no” options at the bottom of the message; these are Google links.
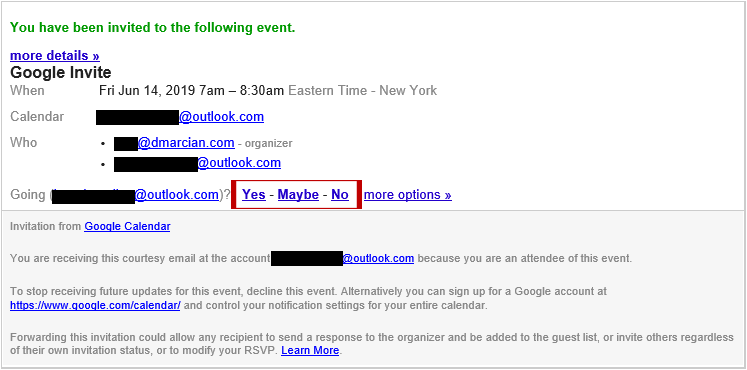
Interacting with the Google links will update the organizer’s calendar and generate an email notification sent by a Google server that spoofs the domain of the invitee. In this case, your domain. Since your domain is protected with DMARC, Google does not technically have permission to send on your behalf, and the email notification delivery fails.
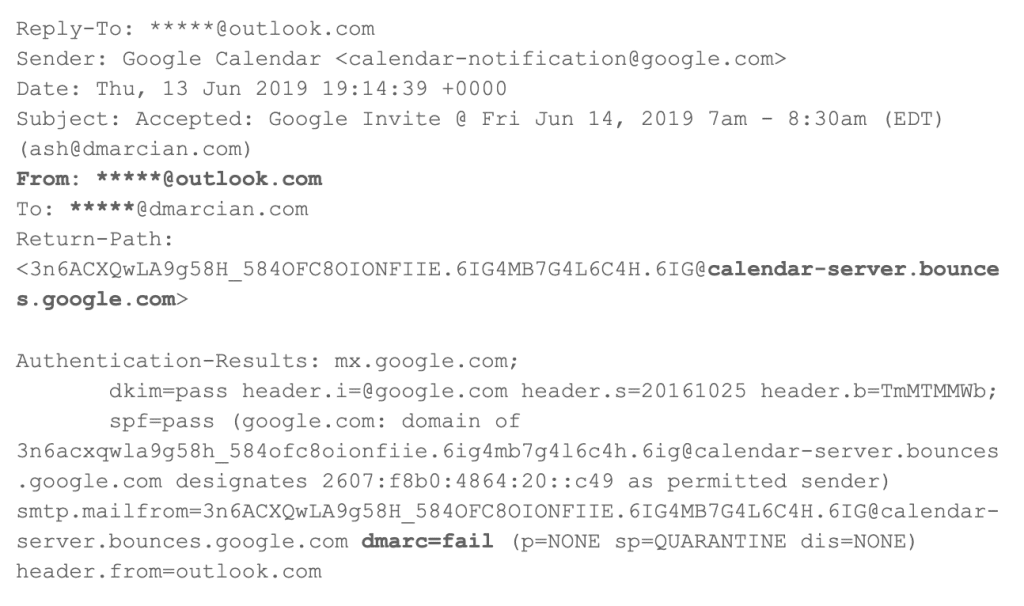
These headers demonstrates how the From: header domain is outlook.com, while the SPF and DKIM identifier belong to the organizational domain google.com. In some instances a bounce may be received if the invitee domain is using a DMARC policy of reject. This can confuse the average user and even email administrators unaware of this behavior.
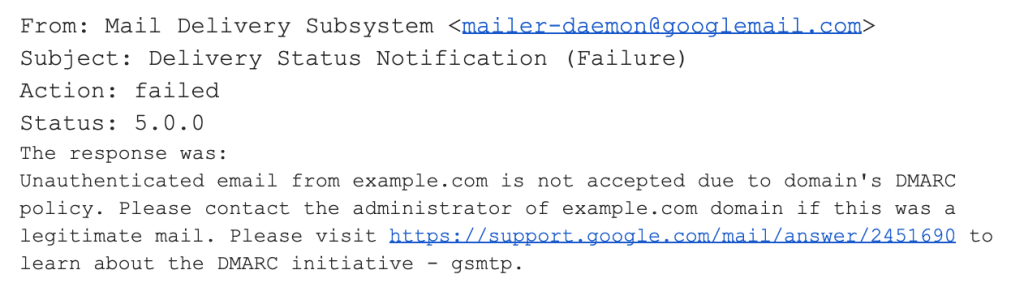
The Solution
A way to circumvent this is to use the functionality provided by your email client to interact with the invite and to ignore the Google links.
The following example was taken from Microsoft Office 2016:
Want to continue the conversation? Head over to the dmarcian Forum.


