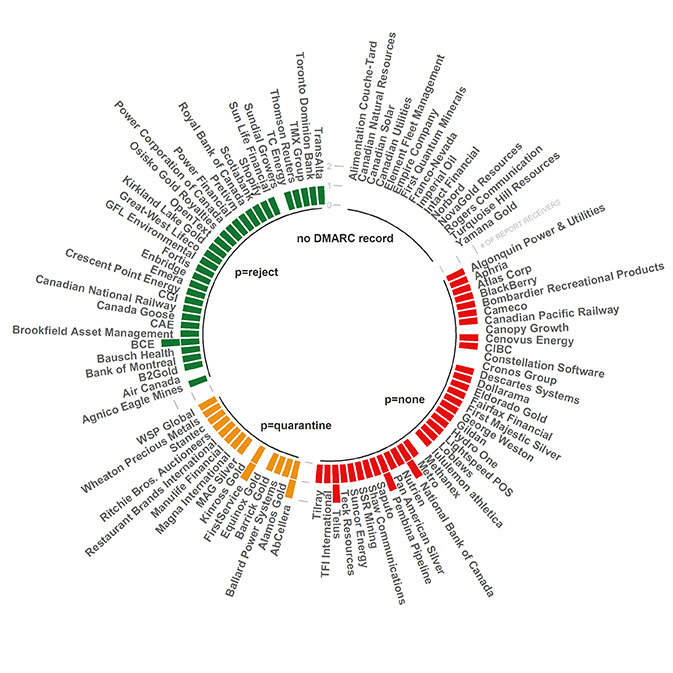
DMARC Status of Top 100 Canadian Companies – Revisited
In June 2021 we published research on DMARC adoption among the top 100 companies in Canada. Twenty months later, we evaluated the DMARC adoption rate and are excited to share those rosy results.
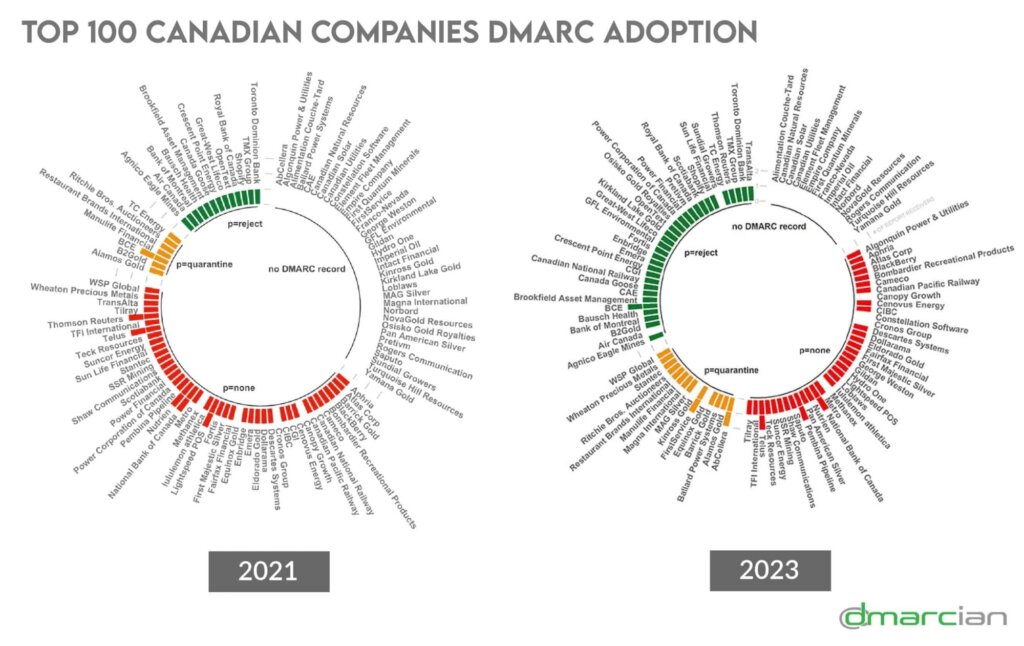
Here’s the DMARC adoption rate comparison for Canada’s top 100 companies, measured in percentage increase or decrease, from June 2021 to February 2023:
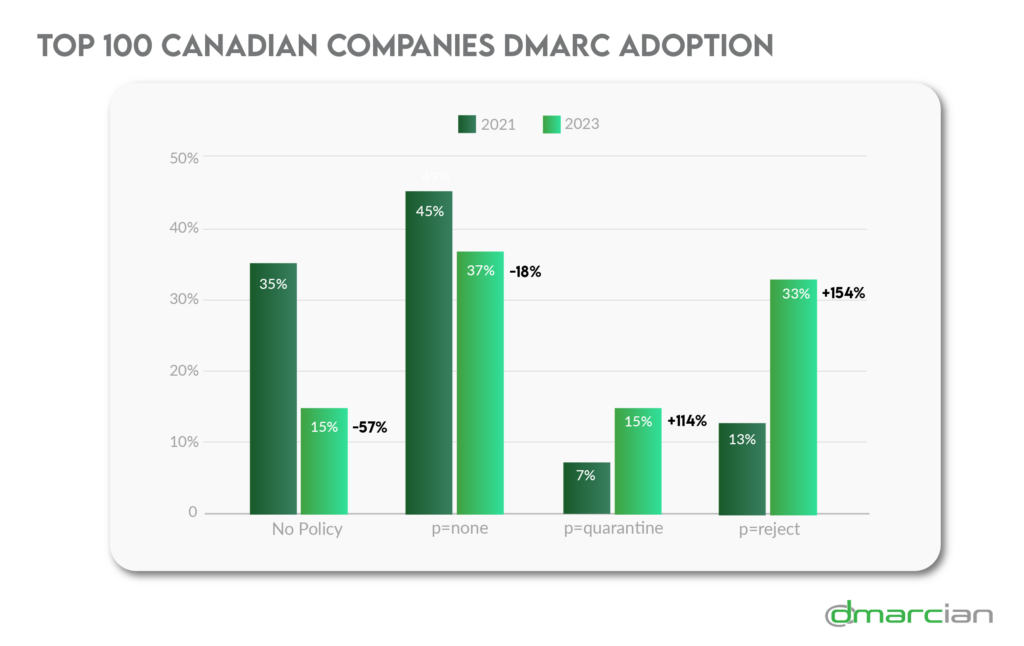
- 154% increase of DMARC policies set to p=reject
- 114% increase of DMARC policies set to p=quarantine
- 18% decrease of DMARC policies set to p=none
- 57% decrease of companies lacking a DMARC policy
Above all, a fifth of the top Canadian companies advanced their DMARC policies to the ultimate goal of a p=reject DMARC policy. With a p=reject policy in place, emails failing DMARC authentication aren’t delivered to the destined inbox.
Another fifth took the initial step in securing their domains by establishing DMARC records. People typically begin their road to DMARC compliance by employing a p=none DMARC policy. This policy turns on the lights, as we like to say, to gain visibility into who and what services are using a particular domain, for good or ill.
“It’s fantastic to see the top Canadian companies taking DMARC seriously,” said Asher Morin, Toronto-based dmarcian Director of Deployment Services. “This adoption should be a clear message to all—it’s useful, it works, and it’s not impossible to deploy. This is a good reminder that the initial cost to get started is low: a single TXT DNS record for your domain(s). That is just the beginning, however. The true goal is to get the policy in reject mode. Everything in between is just a stepping stone to that finish line.”
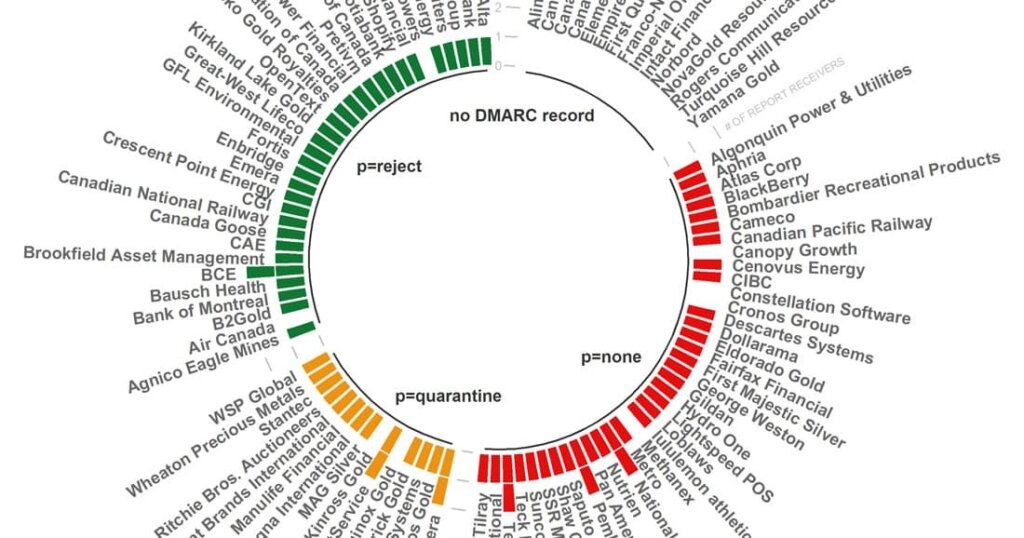
2023 Adoption: Top 100 Canadian Companies
In September 2021, the Canadian Centre for Cyber Security (Cyber Centre) published Ransomware: How to Prevent and Recover which offers guidance on ways organizations can minimize risk and prepare in case a ransomware attack occurs. Establishing and maintaining security tools, including “DMARC, an email authentication and reporting system that helps to protect your organization’s domains from spoofing, phishing, and other malicious activities” are among the preventive measures included.
Additionally, the Cyber Centre’s Implementation Guidance: Email Domain Protection, updated in August 2021, recommends deploying DMARC to protect domains by
- Preventing the delivery of malicious messages impersonating your domains;
- Deterring threat actors from attempting to spoof protected domains;
- Improving the security of email recipients; and
- Protecting the reputation of organizations whose domains are the target of spoofing.
Take a look at DMARC adoption rates for other sectors
“We’ve said it before, but we’ll say it again: now is the time to take cyber security seriously,” said Sami Khoury, Head of the Canadian Cyber Centre. “We hope that Canadians—individuals and organizations alike—will heed our call to action and that, together, we can build a more secure Canada.”
With a team of email security experts and a mission of making email and the internet more trustworthy, dmarcian is here to help assess an organization’s domain catalog and manage DMARC for the long haul. Our Canadian headquarters and data center in Toronto allows us to continue to help Canada-based organizations deploy DMARC and comply with the country’s data sovereignty regulations.